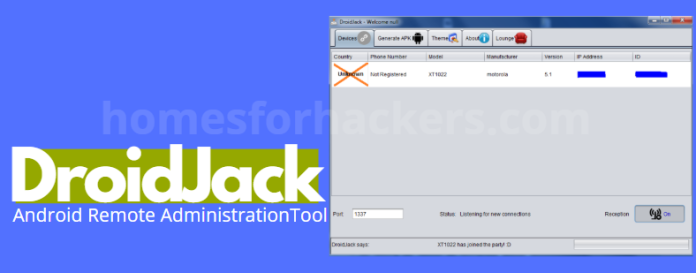
DroidJack is a Remote Access Trojan (RAT – Remote Administration Tool) for Android systems like AndroRAT (Android Trojan) or Dendroid – Android Trojan. While the developers claim that the tool has been developed to protect and control loved ones, many users are misusing it, violating the privacy of other users and stealing all kinds of information from the devices.
Early in the development, the hackers were ordinary developers who published their legitimate remote control tool on the Play Store under the name of Sandroid. Due to its lack of success, they decided to take a not very moral path, which is that they ported the DroidJack engine, formerly known as SandroRAT, and developed with it a malicious tool that soon began to be sold on clandestine hacker forums.
This Trojan has become very active in recent months, especially in Europe, which has drawn the attention of the security forces and bodies of the different countries of the European Union and they have started an offensive against all users who are using this Trojan. Trojan to control smartphones remotely.
At the moment, 13 addresses of DroidJack users have already been registered, and it seems that this number will continue to increase in the coming weeks. As reported by the BBC, arrest campaigns are being carried out against those people who bought the Trojan license (which is not exactly cheap) and who have been using it in various countries such as the United Kingdom, France, Germany, Belgium and Switzerland since its launch in 2014.
DroidJack Features
This Trojan for Android is one of the most complete. With it we will be able to have remote access to the entire infected device, from the calendar, calls and SMS to the microphone and cameras of the smartphone. All.
Among others, the main characteristics of this malicious software are:
- It allows you to hide in any application or game for Android without showing signs of life.
- Full access to file storage, being able to copy data to the PC or from the PC to the device.
- Monitoring and full control over SMS.
- Monitoring and full control over calls.
- Access to the calendar.
- Access to both the earpiece and microphone of the device.
- Browsing history.
- Location tracking.
- Ability to send messages to the device.
- It allows you to control installed applications, running processes, view a list of all of them and run applications on demand.
- Collect information about device connectivity: IMEI, Carrier, Wi-Fi, etc.
- It installs, runs and updates completely hidden.
- All of the above works without root permissions.
DroidJack, the Trojan that is marketed as normal software
We already know that malicious software is sold to hackers on the Deep Web, however, the case of DroidJack is different as well as peculiar. Those responsible for the development of this remote control Trojan sell their tool to any user on the normal network at a price of $210 per license through their website.
The payment of said license can be made both through PayPal and by credit card, which means that when it comes to marketing it, it is like another piece of software, without malicious intent, and that is that, after all, those who misuse his are the buyers, not the developers.
OmniRAT, malware to hack Windows, Android and OS X for only $25
OmniRAT is a new type of malware that picks up where DroidJack left off, and can easily take over Android, Windows, OS X and Linux.
A big one is upon us and no one is safe . As European police manage to eliminate the use of the DroidJack malware , a similar product has emerged that can control not only Android, but also Windows, OS X and Linux and is selling for only a fraction of the cost.
This remote control tool, detected by the security firm Avast, is called OmniRAT and appears to be of German origin. The vendor promises that the “remote administration tool” can operate on smartphones Android, but it will also allow full control on Windows systems and some control on OS X and Unix-based computers after installation.
Avast investigated a code incident for this software in Germany, where the victim received a text message stating that she was unable to display an image because of the current Android Stagefright patch. In order to see it, the victim was asked to download a specific app to do so.
This, of course, should be enough notice . Any software download from an unknown or untrustworthy source should be viewed with caution. Once the app is downloaded, Google’s permissions model also showed a long list of access and privacy privileges that the software required, and yet the victim gave permission to install it.
How does OmniRAT work?
Once installed, OnmiRAT is very, very difficult to remove from the system . Deleting the originally downloaded software is of no use, and the driver of the software has full permission to the device and can make calls, steal files, and remotely control other devices after sending them the code with another text message, something we’ve seen in other cases. mobile malware .
In the words of Nikolaos Chrisaidos , a mobile malware and security analyst at Avast:
We know that data collected by the custom version of OmniRAT that targeted a person of German origin who appeared on the Techboard forum is being sent to a Russian domain, based on the address of the C&C server the data was being sent to. .
What could make the OmniRAT a potentially bigger problem than the DroidJack is its cost. Older malware costs upwards of $200, while OmniRAT, which reuses a lot of its code, only asks $25 for the software and includes a “lifetime guarantee,” though this will likely only last until the police kill it off. .
Chrysaidos has given the following advice to users to protect themselves from OmiRAT:
- Having an antivirus installed on the mobile –although this, as we already know, is not very useful–. Avast antivirus detects this threat as Android:OmniRat-A [Trj]
- Do not open links from sources you do not trust. If an unknown phone number or email address sends us one, please do not open it under any circumstances.
- Use only official sources to download apps .
As always, these are indications in which common sense should prevail . It will always be our best ally to keep our devices safe.
Apart from that, if you are interested to know about DIY Logo: A Step-by-Step Guide then visit our Digital Marketing category.